Sweden’s prosecution authority has reopened a preliminary investigation into Wikileaks founder Julian Assange on an allegation of rape dating back to 2010.
It said today it will issue a European Arrest Warrant for Assange, and submit an application for a detention order to Uppsala District Court — as the suspected crime took place in Enköping municipality.
An earlier attempt by the Swedish prosecution authority to investigate the alleged sex crime was dropped after Assange fled to the Ecuadorian embassy in London, UK, in 2012.
A second sex crime allegation against Assange involving a separate Swedish woman cannot be reopened as the legal time-limit on pursuing a case has been exceeded.
The Wikileaks founder was arrested at the Ecuadorian embassy in London last month, after it withdrew diplomatic asylum. He was then quickly found guilty of breaching his 2012 bail conditions.
A judge at Southwark Crown Court then sentenced him to 50 weeks earlier this month. He is now serving that sentence in a UK prison.
Sweden’s deputy director of public prosecution, Eva-Marie Persson, said today that any conflict between the European Arrest Warrant and an existing US extradition request for Assange will be decided by UK authorities.
It would be up to UK courts — and potentially the home secretary, Sajid Javid — to make a final decision where to send Assange if there are conflicting extradition requests.
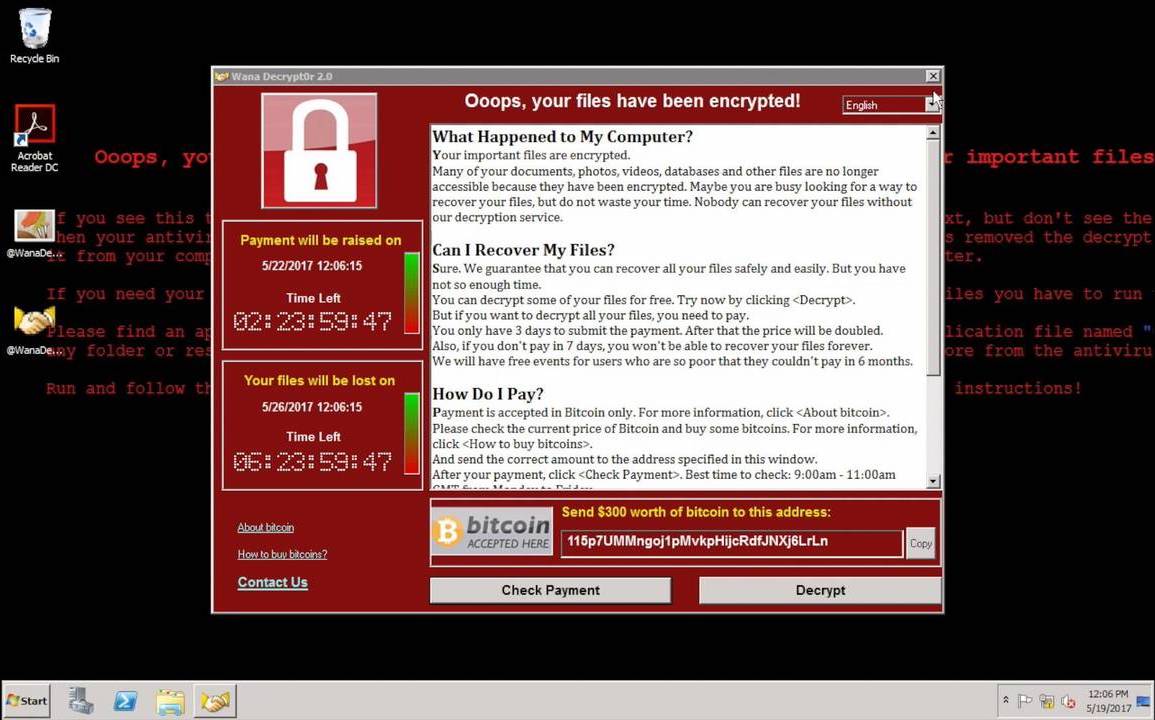
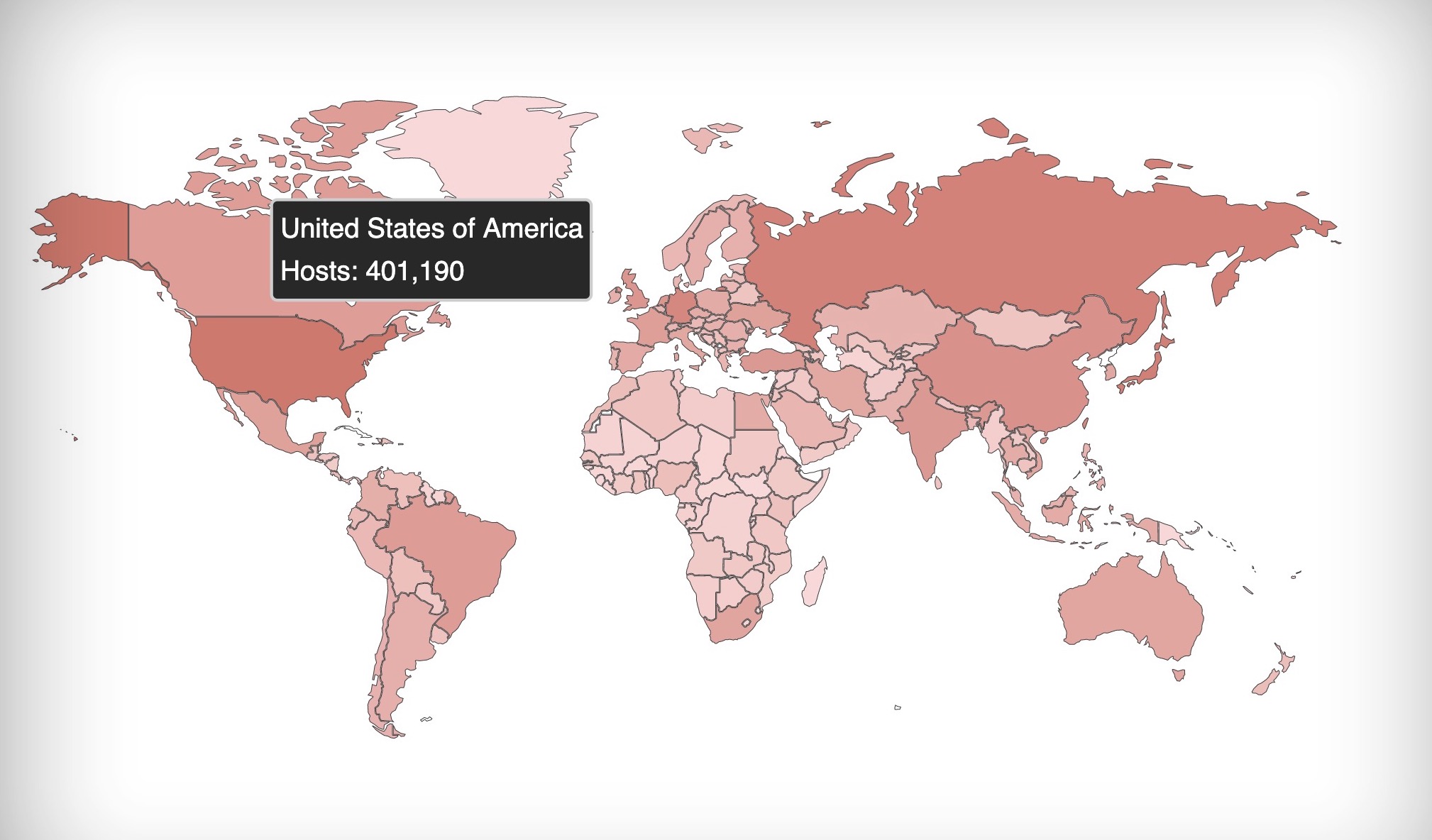
Once in UK police custody last month the Wikileaks founder was also almost immediately rearrested on behalf of the U.S. — which is seeking his extradition on a charge of conspiracy to hack into a classified computer relating to the leaking of military secrets to Wikileaks by whistleblower, Chelsea Manning.
“I am well aware of the fact that an extradition process is ongoing in the UK and that he could be extradited to the US. In the event of a conflict between a European Arrest Warrant and a request for extradition from the US, UK authorities will decide on the order of priority. The outcome of this process is impossible to predict. However, in my view the Swedish case can proceed concurrently with the proceedings in the UK,” said Persson in a statement regarding potential extradition conflict.
In wider comments regarding reopening the case she said simply that circumstances have changed.
“On account of Julian Assange leaving the Ecuadorian embassy, the circumstances in this case have changed. I take the view that there exists the possibility to take the case forward.”
She also noted that UK authorities have told her office Assange must serve 25 weeks of his sentence before he can be released.
Reopening the investigation against Assange means “a number of investigative measures will take place”, she added, suggesting her office could seek to question Assange while he is detained in UK prison — while noting he would have to agree to co-operate with any interview.
“In my opinion a new interview with the suspect is required. It may be necessary, with the support of a European Investigation Order, to request an interview with [Assange] be held in the UK. Such an interview, however, requires [hi]s consent,” she said.
Wikileaks’ editor-in-chief, Kristinn Hrafnsson, has responded to Sweden reopening the rape allegation investigation with a statement in which he claims the country is doing so “under intense political pressure” and that the case “has been mishandled throughout”.
He also denies Assange ever sought to evade the investigation, despite fleeing to and remaining within the Ecuadorian Embassy for seven years, and suggests that a fresh investigation “will give Julian a chance to clear his name”.
In a statement in UK court ahead of his sentencing for breaching bail conditions Assange apologized “unreservedly to those who consider that I have disrespected them by the way I have pursued my case”, adding that he regretted his decision to flee.
“Assange was always willing to answer any questions from the Swedish authorities and repeatedly offered to do so, over six years. The widespread media assertion that Assange ‘evaded’ Swedish questioning is false,” Hrafnsson writes now, leaving little wiggle room should Assange decline to be interviewed by Swedish prosecutors while behind bars in the UK.
Last month a cross-party coalition of 70 UK MPs wrote to the home secretary calling for him to “champion action” to ensure Assange is extradited to Sweden should prosecutors request it, as they now have.
Their letter called for Javid to “stand with the victims of sexual violence and seek to ensure the case against Mr Assange can now be properly investigated”, to ensure “due process” is followed for the complainant.
Parliamentarians also pointed out that the legal expiry date in this case of alleged rape is August 2020, meaning there’s only a short window to take a case against Assange to court — arguing that the Swedish prosecutors should therefore be given priority in any extradition conflict with the US.
Assange is challenging the US extradition request — appearing at a court hearing May 2, via videolink, to say he did not consent to being sent to the US, per the Guardian, while the court heard that the extradition process would take “many months”.